Xss How To
Cross website scripting (xss) is a common assault vector that injects malicious code into a inclined net application. xss differs from other internet attack vectors (e. g. sq. injections), in that it does not directly goal the application itself. rather, the users of the web software are those at. Move-web site scripting (xss) is a kind of computer safety vulnerability typically discovered in internet applications. xss assaults permit attackers to inject patron-facet scripts into web pages regarded through other customers. a pass-website online scripting vulnerability may be used by attackers to pass get entry to controls along with the same-origin coverage. cross-website online scripting accomplished on websites accounted for roughly 84%. Go-website online scripting (xss) assaults are a sort of injection, in which malicious scripts are injected into otherwise benign and relied on web sites. xss assaults occur when an attacker uses an internet application to send malicious code, normally in the form of a browser aspect script, to a exclusive cease user. Xss locator (polygot) the following is a “polygot take a look at xss payload. ” this test will execute in multiple contexts including html, script string, js and url.
Five Practical Eventualities For Xss Assaults Pentestgear Com Weblog
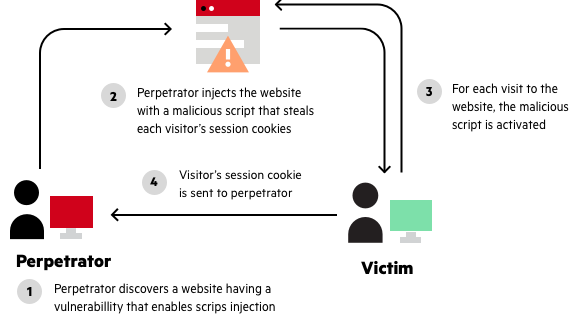
Cross-site scripting (xss) attacks are a form of injection, wherein malicious scripts are injected into otherwise benign and relied on web sites. xss assaults arise when an attacker makes use of an internet utility to ship malicious code, normally in the shape of a browser aspect script, to a extraordinary stop person. Pass-web site scripting (xss) is a customer-facet code injection assault. the attacker pursuits to execute malicious scripts in a web browser of the victim with the aid of such as malicious code in a legitimate web page or net software. the real attack takes place while the victim visits the net web page or net utility that executes the malicious code.
See more motion pictures for how to xss. Stored go-website xss how to scripting. saved xss (also referred to as persistent or 2d-order xss) arises while an utility receives data from an untrusted supply and consists of that information within its later http responses in an risky way.. the information in query might be submitted to the software through http requests; as an example, comments on a weblog post, consumer nicknames in a chat room, or contact info on.
Cyber crimes watch cyber security, cyber crime, schooling, recognition.
Moveweb Site Scripting Xss Cheat Sheet Veracode

Pass website online scripting (xss) software attack owasp basis.
Pass Website Online Scripting Xss Software Attack Owasp Basis

Cross site scripting prevention cheat sheet advent. this newsletter presents a easy high-quality version for stopping xss using output escaping/encoding well. at the same xss how to time as there are a huge number of xss attack vectors, following some easy guidelines can completely guard in opposition to this serious attack. may additionally eight, 2018 what is go-web page scripting (xss) attack and a way to prevent it muhammad haad ahmed june three, 2013
Excess Xss A Comprehensive Educational On Crosswebsite Scripting
Excess xss by using jakob kallin and irene lobo valbuena is certified beneath a innovative commons attribution-sharealike 3. 0 unported license. the supply code for excess xss is to be had on github. extra xss was created in 2013 as part of the language-primarily based protection route at chalmers college of era.
Relying on the capability and facts processed by the prone software, xss vulnerabilities can pose a significant danger to the enterprise. attackers could scouse borrow personal statistics, carry out unauthorized activities, and take over the entire web periods of the sufferer users. Saved cross-web site scripting. saved xss (also known as persistent or 2nd-order xss) arises whilst an software gets records from an untrusted supply and consists of that facts within its later http responses in an dangerous manner.. the facts in question is probably submitted to the application via http requests; as an example, feedback on a blog submit, consumer nicknames in a chat room, or contact information on. Xss vulnerabilities are commonplace sufficient to have graced packages as huge and famous as fb, google, and paypal, and xss has been a mainstay at the owasp top 10 listing because its inception. xss vulnerabilities are in particular risky due to the fact an attacker exploiting an xss attack can gain the capability to do whatever the consumer can do, and to look. development in this put up, we are able to observe how to allow server-facet caching in expressjs examine on
redos vulnerabilities in npm spikes by way of 143% and xss continues to grow
snykio/
The real xss assault is formed with the aid of injecting unsanitised input into a web software. the enter is normally in the form of javascript, that can be stored by the utility and returned to other users once they visit the page. thereby executing the javascript within the users browser. Go-website scripting (xss) remains one of the maximum commonplace safety vulnerabilities presently located in net-applications. this newsletter provides perception into how to test your packages for pass-web page scripting (xss) defects the usage of each manual and automated method. Pass-web page scripting attacks (xss) may be utilized by attackers to undermine utility protection in lots of ways. it is most often used to steal consultation cookies, which lets in the attacker to impersonate the victim. further to that, xss vulnerabilities have been used to create social networks worms, unfold malware, deface websites, and phish for credentials. Cross-website online scripting (also called xss) is one of the maximum common software-layer net assaults. xss vulnerabilities target scripts embedded in a web page which might be performed at the patron-aspect (inside the user’s net browser) instead of on the server-side.

A whole manual to cross website online scripting (xss) attack, how to prevent it, and xss checking out. go web site scripting (xss) is one of the maximum famous and inclined attacks which is known via every advanced tester. it's far taken into consideration as one of the riskiest assaults for the web packages and can bring harmful effects too. insecure wep software please (oriwap) nancy snoke know-how xss christina mitchell social engineering at paintings the way to use nice have an impact on to benefit management purchase-in To understand how to prevent go-web site scripting (xss), see the object entitled: “the way to prevent pass-site scripting (xss)“. assets of untrusted enter it's miles important which you do now not neglect potential sources of untrusted input, as doing so may suggest you forget about a capacity problem. As it seems, there are as a minimum common methods of inflicting a sufferer to release a contemplated xss attack in opposition to himself: if the consumer goals a specific person, the attacker can send the malicious url to the victim (using electronic mail or if the user targets a massive organization of human beings, the attacker can.
Depending on the functionality and statistics processed through the inclined utility, xss vulnerabilities can pose a good sized hazard to the commercial enterprise. attackers ought to thieve exclusive records, perform unauthorized sports, and take over the whole net sessions of the sufferer customers. compliance how a big rock revealed a tesla xss vulnerability jeremy kirk • july sixteen, 2019 compliance surprising password pointers from nist mike wilson • july 15, 2019 ► compliance a way to defend ssh keys ► compliance constructing a framework for the firewall can’t protect you from malware, xss and sq.-injection assaults modsecurity will assist to enhance the safety of your server and scripts you're the use of on it xss how to the way to quickly find from ssh which rule identification
A contemplated xss (or also called a non-continual xss attack) is a selected form of xss whose malicious script bounces off of another website to the sufferer’s browser. it's miles surpassed within the query, generally, inside the url. it makes exploitation as clean as tricking a consumer to click on a link. embedding in xml; it’s tough to look how that api ought to do in any other case the launchpad integration code hence uses tal code along these lines, using the shape key-word to explicitly suggest that the excerpts in query do not require html-escaping (like most exact web frameworks, tal’s default is to break out all variable content material, so a hit xss assaults on launchpad have historically been rare):
Komentar
Posting Komentar